Quantum Key Distribution (QKD) protocols are performed by sending a sizeable, but finite, number of quantum signals between the distant parties involved. Many QKD experiments, however, predict their achievable key rates using asymptotic formulas, which assume the transmission of an infinite number of signals, partly because QKD proofs with finite transmissions (and finite-key lengths) can be difficult.
A team of researchers at MIT and Raytheon has developed a robust numerical approach for calculating the key rates for QKD protocols in the finite-key regime in terms of two Semi-Definite Programs (SDPs).
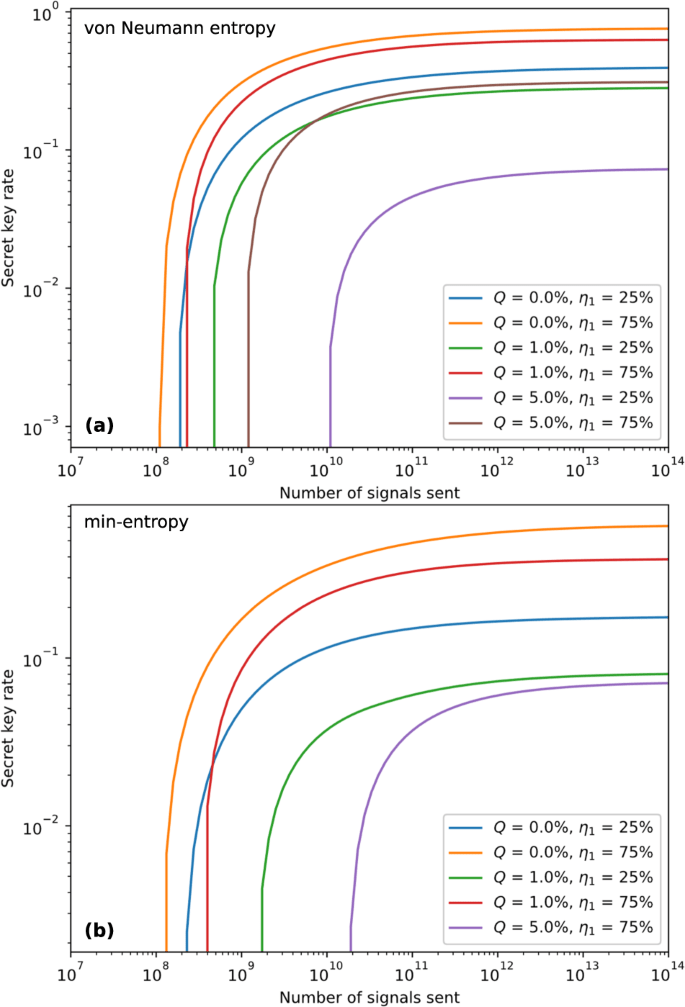
The first uses the relation between conditional smooth min-entropy and quantum relative entropy through the quantum asymptotic equipartition property, and the second uses the relation between the smooth min-entropy and quantum fidelity. The numerical programs are formulated under the assumption of collective attacks from the eavesdropper and can be promoted to withstand coherent attacks using the postselection technique.
They solved these SDPs using convex optimization solvers and obtain numerical calculations of finite-key rates for several protocols difficult to analyze analytically, such as BB84 with unequal detector efficiencies, B92, and twin-field QKD.
This numerical approach democratizes the composable security proofs for QKD protocols where the derived keys can be used as an input to another cryptosystem.
The work has been published in npj quantum information.
